Completed
Part11: Web User Identification: Forensic Database Analysis
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
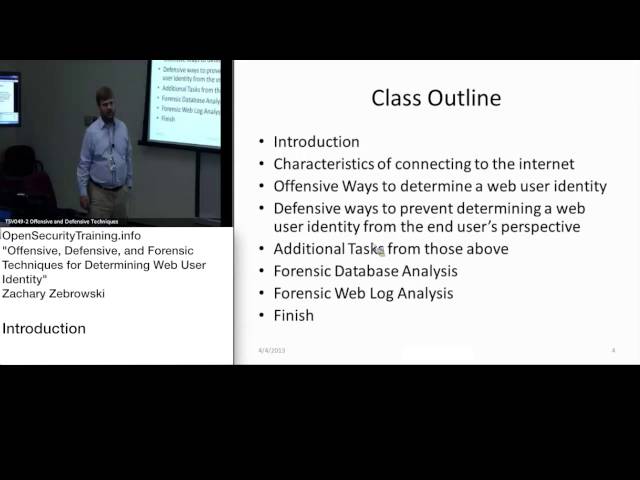
Offensive, Defensive, and Forensic Techniques for Determining Web User Identity
Automatically move to the next video in the Classroom when playback concludes
- 1 Part1: Web User Identification: Intro
- 2 Part2: Web User Identification: Characteristics Of Internet Connections
- 3 Part3: Web User Identification: IP Geolocation
- 4 Part4: Web User Identification: Browser Identification
- 5 Part5: Web User Identification: Borrowing Wifi Connections
- 6 Part6: Web User Identification: Shell & Cloud Accounts
- 7 Part7: Web User Identification: Anonymizers
- 8 Part8: Web User Identification: Web Browser Privacy Modes
- 9 Part9: Web User Identification: Email Origin Obfuscation
- 10 Part10: Web User Identification: Further Web Browser Attacks & Defenses
- 11 Part11: Web User Identification: Forensic Database Analysis
- 12 Part12: Web User Identification: Forensic Log Analysis