Completed
Packet Traveling - How Packets Move Through a Network
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Complete Practical Networking Course - Packet Traveling, Subnetting, VLANs, Cryptography, and NAT
Automatically move to the next video in the Classroom when playback concludes
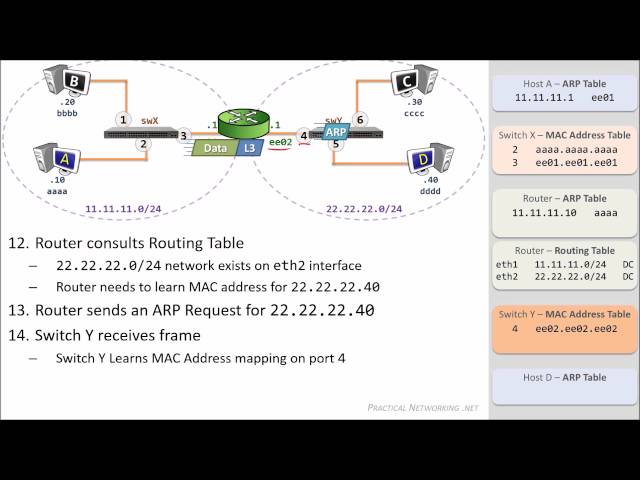
- 1 Packet Traveling - How Packets Move Through a Network
- 2 Address Resolution Protocol (ARP) in less than 5 minutes
- 3 What is Subnetting? - Subnetting Mastery - Part 1 of 7
- 4 Drawing the Cheat Sheet - Subnetting Mastery - Part 2 of 7
- 5 How to solve ANY Subnetting Problems in 60 seconds or less - Subnetting Mastery - Part 3 of 7
- 6 Practice Examples - Subnetting Mastery - Part 4 of 7
- 7 Time-Saving Tricks for Subnetting - Subnetting Mastery - Part 5 of 7
- 8 Subnetting in the /17 - /24 range - Subnetting Mastery - Part 6 of 7
- 9 Subnetting in the /1 - /16 range - Subnetting Mastery - Part 7 of 7
- 10 Fixed-Length Subnet Mask (FLSM) - Subnetting Mastery - FLSM and VLSM Appendix Part 1 of 2
- 11 Variable-Length Subnet Mask (VLSM) - Subnetting Mastery - FLSM and VLSM Appendix Part 2 of 2
- 12 Native VLAN - the DEFINITIVE illustration
- 13 What are VLANs? -- the simplest explanation
- 14 Route Precedence -- How does a Router choose a path when multiple paths exist?
- 15 Route Precedence -- Answer to Bonus Questions
- 16 Local Broadcast and Directed Broadcasts - Description and Demonstration
- 17 Local Broadcast and Directed Broadcasts - Demo and Packet Captures
- 18 🎬 Packet Tracer challenge: Find the Imposter - Layer 2
- 19 🎬 Packet Tracer challenge: Find the Imposter - Layer 2 - SOLUTION VIDEO
- 20 Hashing, Hashing Algorithms, and Collisions - Cryptography - Practical TLS
- 21 Data Integrity - How Hashing is used to ensure data isn't modified - HMAC - Cryptography
- 22 Facebook went down!! Let's use that to talk about BGP, DNS, and Anycast
- 23 Encryption - Symmetric Encryption vs Asymmetric Encryption - Cryptography - Practical TLS
- 24 Public and Private Keys - Signatures & Key Exchanges - Cryptography - Practical TLS
- 25 How SSL & TLS use Cryptographic tools to secure your data - Practical TLS
- 26 Public Key Infrastructure - What is a PKI? - Cryptography - Practical TLS
- 27 RSA Algorithm - How does it work? - I'll PROVE it with an Example! -- Cryptography - Practical TLS
- 28 Diffie-Hellman Key Exchange - the MAGIC that makes it possible - Cryptography - Practical TLS
- 29 TLS / SSL - The complete sequence - Practical TLS
- 30 How does NAT conserve IP Address Space? (and why!) - Network Address Translation
- 31 Static NAT - Network Address Translation
- 32 Dynamic PAT - Network Address Translation
- 33 Dynamic NAT - Network Address Translation
- 34 Policy NAT - Network Address Translation
- 35 Twice NAT - Network Address Translation
- 36 OpenSSL - Encrypting and Decrypting Private Key Files