Completed
Identifying Memory Locations
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Detecting Attacks Against Robotic Vehicles - A Control Invariant Approach
Automatically move to the next video in the Classroom when playback concludes
- 1 Intro
- 2 Robotic Vehicles (RVS)
- 3 Cyber vs. Physical Attacks
- 4 Attack Model
- 5 Our Control Invariant (CI) Approach
- 6 Control Invariant Extraction
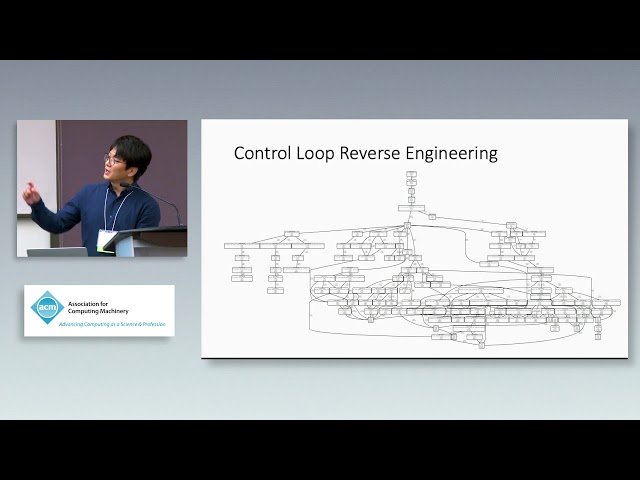
- 7 Control Loop Reverse Engineering
- 8 Identifying Memory Locations
- 9 Monitoring Parameter Selection
- 10 Evaluation: Subject Vehicles
- 11 Simulated Attacks
- 12 Evaluation: Effectiveness
- 13 Evaluation: Efficiency
- 14 Case Study
- 15 Conclusion