Free Online
Timing Attacks Courses and Certifications
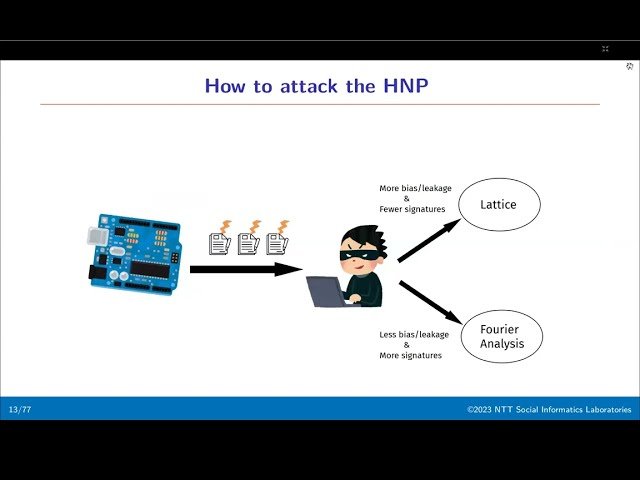
Discover how attackers exploit timing variations in cryptographic systems and web applications to extract sensitive data. Learn practical exploitation techniques, countermeasures, and real-world attack scenarios through security conference talks and demonstrations on YouTube from Black Hat, DEFCON, and OWASP.
Showing 64 courses
Filter by
Filters
-
-
Level
-
Duration
-
Language
-
-
- YouTube
- 22 minutes
- Self-Paced
- Free Video
-
- YouTube
- 14 minutes
- Self-Paced
- Free Video
-
- YouTube
- 28 minutes
- Self-Paced
- Free Video
-
- YouTube
- 14 minutes
- Self-Paced
- Free Video
-
- YouTube
- 50 minutes
- Self-Paced
- Conference Talk
-
- YouTube
- 43 minutes
- Self-Paced
- Free Video
-
- YouTube
- 34 minutes
- Self-Paced
- Free Video
-
-
- YouTube
- 55 minutes
- Self-Paced
- Conference Talk
-
- YouTube
- 39 minutes
- Self-Paced
- Conference Talk
-
- YouTube
- 35 minutes
- Self-Paced
- Conference Talk
-
- YouTube
- 1 hour 12 minutes
- Self-Paced
- Free Video
-
- YouTube
- 42 minutes
- Self-Paced
- Free Video
-
- YouTube
- 39 minutes
- Self-Paced
- Free Video
-
- YouTube
- 21 minutes
- Self-Paced
- Free Video
-
- TrainSec
- Self-Paced
- Paid Course
-