Free Online
Kerberoasting Courses and Certifications
Learn how attackers exploit Kerberos authentication in Active Directory environments through kerberoasting techniques. Gain hands-on skills in penetration testing, bypassing defenses, and post-exploitation using real-world tools and scenarios, with practical tutorials from experts on YouTube and Cybrary. Ideal for cybersecurity beginners and aspiring ethical hackers.
Showing 12 courses
Filter by
Filters
-
-
Level
-
Duration
-
Language
-
-
- Cybrary
- Self-Paced
- Paid Course
-
- YouTube
- 1 hour 33 minutes
- Self-Paced
- Free Video
-
- YouTube
- 22 minutes
- Self-Paced
- Conference Talk
-
- YouTube
- 26 minutes
- Self-Paced
- Free Video
-
- YouTube
- 55 minutes
- Self-Paced
- Conference Talk
-
- YouTube
- 39 minutes
- Self-Paced
- Conference Talk
-
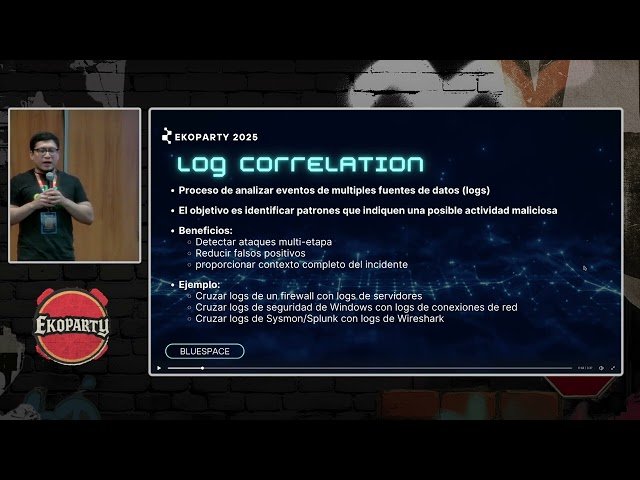
- YouTube
- 50 minutes
- Self-Paced
- Conference Talk
-
-
- YouTube
- 1 hour 28 minutes
- Self-Paced
- Free Video
-
- YouTube
- 1 hour 11 minutes
- Self-Paced
- Free Video
-
- YouTube
- 30 minutes
- Self-Paced
- Free Video
-
- YouTube
- 1 hour 55 minutes
- Self-Paced
- Free Video
-
- YouTube
- 1 hour 11 minutes
- Self-Paced
- Free Video
-