Completed
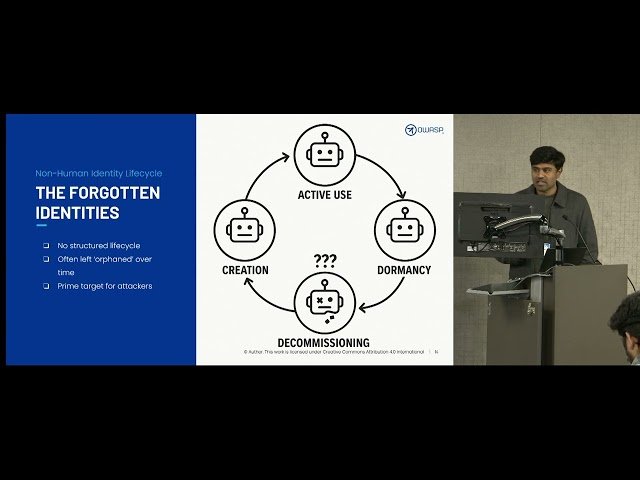
Securing Access: Leveraging IGA, JIT & Policy Controls to Tackle OWASP Threats
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Securing Access - Leveraging IGA, JIT and Policy Controls to Tackle OWASP Threats
Automatically move to the next video in the Classroom when playback concludes