Completed
Tips
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Node.js Application Insecurity - OWASP AppSec California 2015
Automatically move to the next video in the Classroom when playback concludes
- 1 Intro
- 2 Agenda
- 3 Not chance
- 4 Target audience
- 5 What is NoDot
- 6 Why NoDot
- 7 Frameworks
- 8 Categories
- 9 Crosssite scripting
- 10 escaping code
- 11 escape modules
- 12 secret section
- 13 user input
- 14 query language
- 15 use prepared statements
- 16 portrait protection
- 17 false opening
- 18 headers
- 19 classic
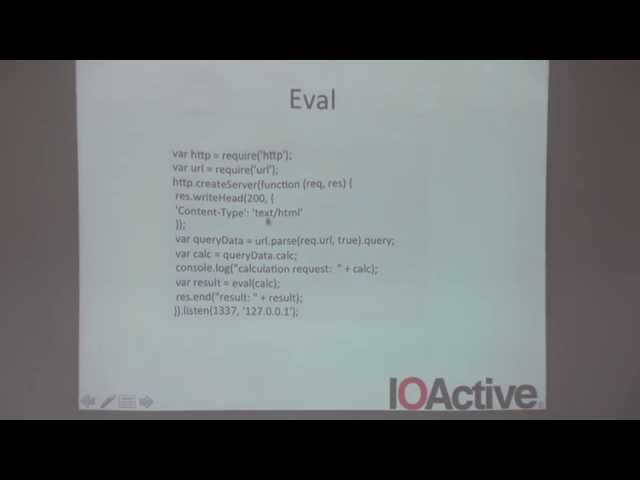
- 20 eval
- 21 exit method
- 22 GitHub example
- 23 Tips
- 24 Record diversity
- 25 Not my test
- 26 Random numbers
- 27 Random bytes
- 28 Pseudorandom
- 29 Rocket
- 30 Stupid Dancer
- 31 Im tutoring area
- 32 Openness
- 33 Documentation
- 34 The problem
- 35 Honey success
- 36 Buffer class
- 37 Buffer
- 38 ReadWrite
- 39 Buffer Overflow
- 40 Watch out allocations
- 41 Summary
- 42 Conclusion