Completed
Introduction
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Narcos, Counterfeiters and Scammers - An Approach to Visualize Illegal Markets
Automatically move to the next video in the Classroom when playback concludes
- 1 Introduction
- 2 Background
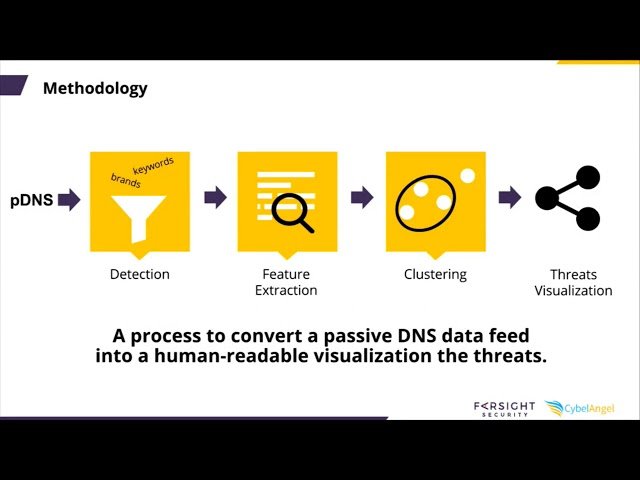
- 3 Breach Landscape
- 4 Passive DNS
- 5 Traditional DNS
- 6 What are we interested in
- 7 What is passive DNS
- 8 Presentation
- 9 Software Architecture
- 10 Keywords
- 11 Keyword Matching
- 12 DNS Twist
- 13 Home Page
- 14 Feature Extraction
- 15 Analytics ID
- 16 Banking ID
- 17 Research Goals
- 18 Naturalistic Approach
- 19 Graphs
- 20 Jeffy
- 21 Network Specialization
- 22 big problems
- 23 an odd
- 24 Clusters
- 25 Traffic Estimation
- 26 Use Case
- 27 Global Overview
- 28 Target the Center
- 29 Cannabis
- 30 Two takeaways
- 31 Conclusion