Completed
57:03 Conclusion
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
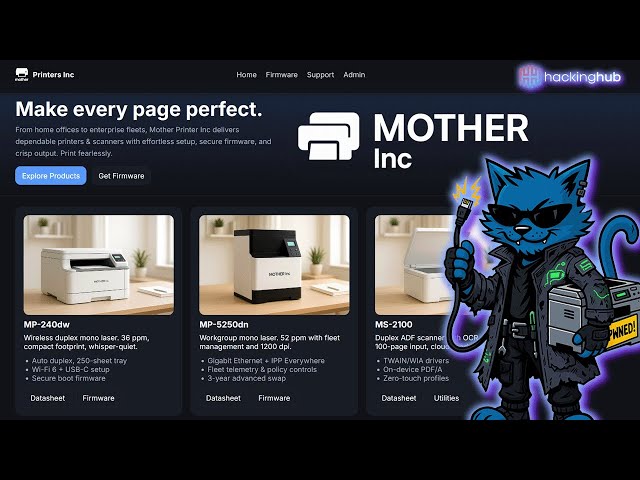
Mother Printers - Full Exploit Chain Analysis and Demo
Automatically move to the next video in the Classroom when playback concludes
- 1 0:00 Introduction
- 2 1:04 Open directory listing exposed secrets
- 3 2:27 Basic file checks
- 4 5:30 Static analysis
- 5 10:05 Info leak serial number
- 6 10:36 Authentication bypass password derivation
- 7 22:36 Unintended solution patched
- 8 24:22 Understanding the flow
- 9 26:54 Obtaining a CSRF token
- 10 28:23 Renaming functions/variables ghidra
- 11 39:46 Buffer overflow referer header
- 12 40:45 Crafting an exploit
- 13 46:55 Debugging bad chars
- 14 50:34 Successful exploit 3 byte overwrite
- 15 52:43 SSRF on admin endpoint XML
- 16 55:01 PoC full chain
- 17 56:40 Summary TL;DR
- 18 57:03 Conclusion