Completed
+ Checking How Outsiders See You
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Intrusion Hunting for the Masses - A Practical Guide
Automatically move to the next video in the Classroom when playback concludes
- 1 Introduction
- 2 What Works Finding Intrusions?
- 3 What Do I Mean by "Hunting"?
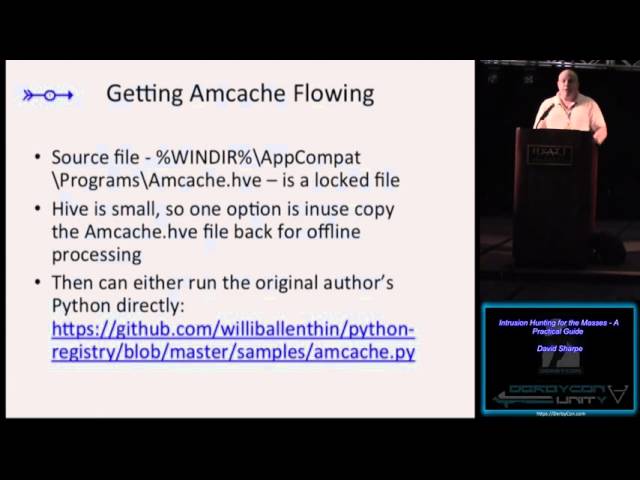
- 4 Shimcache/Amcache
- 5 Shimcache Examples
- 6 What to Look for in the Shimcache/ Amcache Data
- 7 Server Antivirus Logs
- 8 Mining Netstat Data
- 9 User-Agent strings
- 10 User-Agent examples
- 11 o. Windows Services Example
- 12 + Windows Drivers Example
- 13 Windows Autoruns
- 14 Autoruns - Examples
- 15 Windows Prefetch
- 16 Prefetch Examples
- 17 + Checking How Outsiders See You
- 18 NTFS Extended Attributes
- 19 EMET Log Mining - Example
- 20 Hunting in RAM dumps
- 21 Closing Thoughts
- 22 Questions?