Completed
Introduction
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Knowing the Enemy - Creating a Cyber Threat Actor Attribution Program
Automatically move to the next video in the Classroom when playback concludes
- 1 Introduction
- 2 Morse Code
- 3 Sun Tzu
- 4 Program
- 5 Customers want more
- 6 spear phishing
- 7 business email compromise
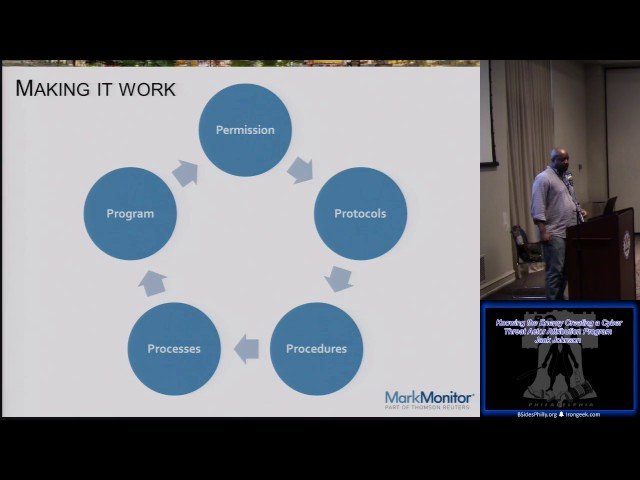
- 8 make it work
- 9 this is getting to
- 10 social engineering
- 11 whats a fish
- 12 stats
- 13 numbers
- 14 monitoring
- 15 data sources
- 16 attribute attribution
- 17 poker tells
- 18 behaviors and habits
- 19 human limitations
- 20 resources
- 21 attack habits
- 22 attribution
- 23 forensic evidence
- 24 collecting too much
- 25 extracting the files
- 26 common strings
- 27 spreadsheet
- 28 mount ego
- 29 investigative tools
- 30 hacker dread