Completed
Kernel Interface Diversification
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Moving Target Defense - Evasive Maneuvers in Cyberspace
Automatically move to the next video in the Classroom when playback concludes
- 1 Introduction
- 2 Attack Patterns
- 3 Security Design Principle of Adequate Protection
- 4 A Hopeless Defense
- 5 Why Do Vulnerable Assets Escape Exploitation and Compromise?
- 6 Moving Target Defense
- 7 Managing the Attack Surface
- 8 Address Space Layout Randomization (ASLR)
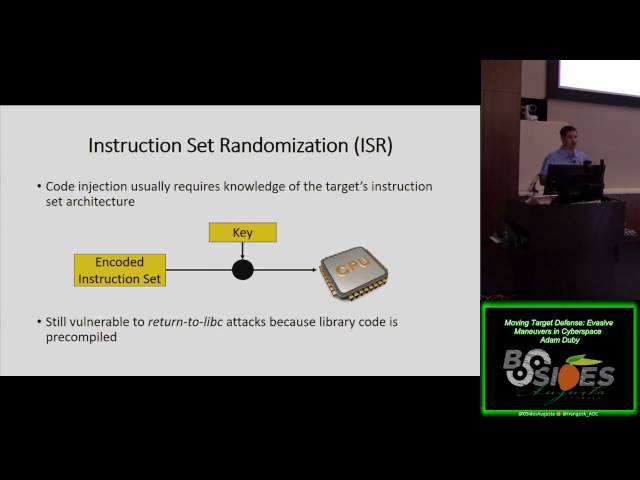
- 9 Instruction Set Randomization (ISR)
- 10 Kernel Interface Diversification
- 11 Compiler-Generated Diversity
- 12 Data Structure Layout Randomization
- 13 The Entropy Problem
- 14 Scalable Binary Diversification
- 15 Theoretical framework for an MTD Strategy
- 16 Resistance to MTD Strategy
- 17 Discussion