Completed
GeeCON 2024: P. Węgrzynowicz - The Hacker’s Guide to Insecure Workload Configuration in Kubernetes
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
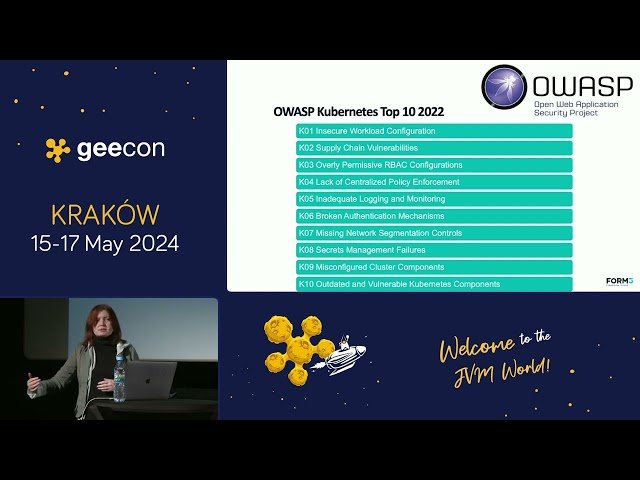
The Hacker's Guide to Insecure Workload Configuration in Kubernetes
Automatically move to the next video in the Classroom when playback concludes