Completed
Exploiting Vulnerable ZK in Ethereum (RWC 2025)
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
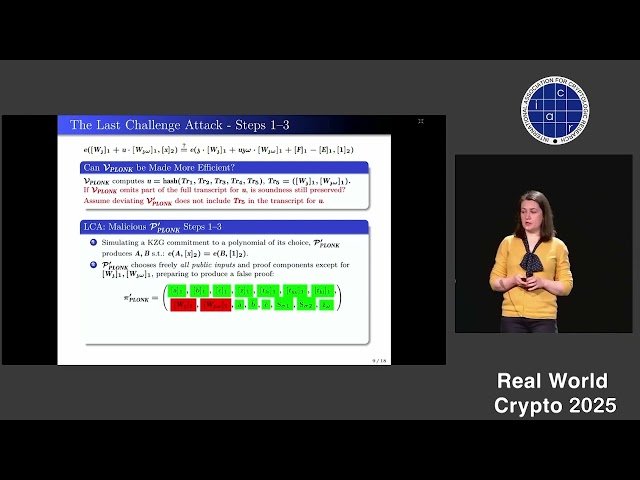
Exploiting Vulnerable Implementations of ZK-based Cryptographic Schemes Used in the Ethereum Ecosystem
Automatically move to the next video in the Classroom when playback concludes