Completed
What is Detokenization? Table Method
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Cybersecurity vs. Tokenization
Automatically move to the next video in the Classroom when playback concludes
- 1 Intro
- 2 Cybersecurity vs. Tokenization - Agenda
- 3 Who Wants Tokenization and Where?
- 4 When Can It Be Used?
- 5 What is Detokenization? Encryption Method
- 6 What is Detokenization? MAC Method
- 7 What is Detokenization? Table Method
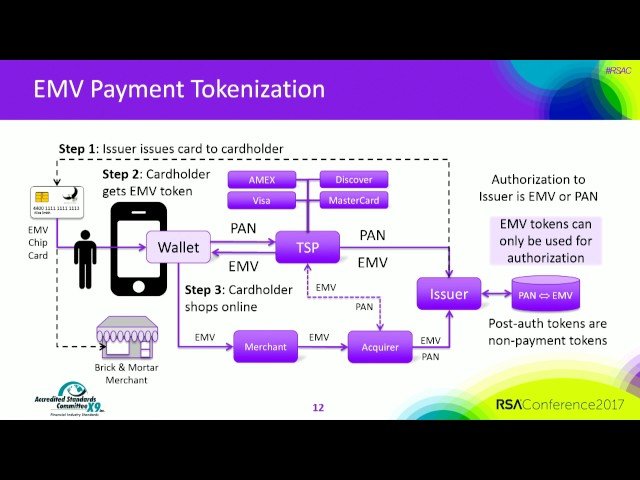
- 8 EMV Payment Tokenization
- 9 Non-Payment Tokenization
- 10 Tokenization Environments: Internal
- 11 Tokenization Environments: Multiple
- 12 Tokenization Isolation
- 13 Cryptography: Encryption Method
- 14 Cryptography: MAC Method
- 15 Cryptography: Random Method
- 16 Cryptography: Table Method
- 17 Apply What You've Learned Today...
- 18 Conclusions
- 19 References