Completed
Why this research?
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Computrace Backdoor Revisited
Automatically move to the next video in the Classroom when playback concludes
- 1 Intro
- 2 Where is Computrace?
- 3 Why this research?
- 4 How does it work?
- 5 Suspicious Behavior
- 6 VT Detection Rate
- 7 Attacks on Protocol
- 8 Small Agent Protocol
- 9 Communication explained
- 10 Vulnerable Protocol Design
- 11 Demo Environment
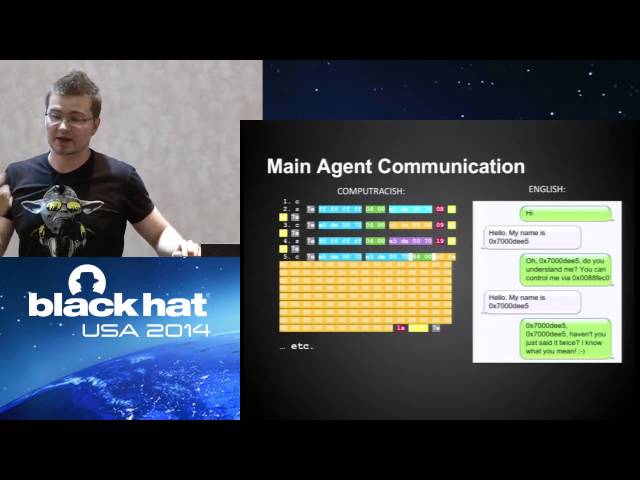
- 12 Main Agent (rpcnet.exe)
- 13 Main Agent Communication
- 14 Vulnerable Protection Mechanism
- 15 Local attacks - Configuration Block
- 16 How to detect Computrace?
- 17 How about network detection?
- 18 Who activated Computrace?
- 19 How to deactivate Computrace?
- 20 Some advice
- 21 Similar Case: Radmin