Completed
Intro
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Automating Bulk Intelligence Collection
Automatically move to the next video in the Classroom when playback concludes
- 1 Intro
- 2 When Automation is Needed?
- 3 What to Automate?
- 4 Planning Automation for Data Mining
- 5 Finding Needle in a Hayshack
- 6 Prepare Checklist of Desired Results
- 7 Consider Inserting Data in a Database!
- 8 Start with Manual Analysis
- 9 Extracting Data from Malware Files
- 10 Analyze Body of Email
- 11 Analyze json File with mime
- 12 Extracting Malicious Domains from wsf file!
- 13 Process of Analyzing Json Mime File Download Json Mime
- 14 Detect the First Chain!
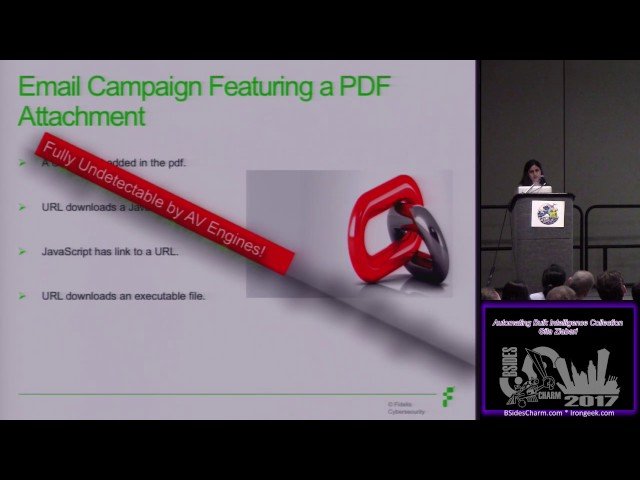
- 15 Email Campaign Featuring a PDF Attachment
- 16 Extract URL from PDF
- 17 CVE-2017-0199 Malicious RTF Document
- 18 Use Known Tools for Analysis
- 19 Apply Foremost on the File!
- 20 Malicious Extracted Files
- 21 Introducing Yalda!
- 22 Yalda Framework
- 23 Data Storage File Type
- 24 Applying Quality Control
- 25 Conclusion
- 26 How to use Yalda
- 27 Code is available at Fidelis gitHub