Completed
Life Cycle
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
Beyond ‘Check The Box’ - Powering Intrusion Investigations
Automatically move to the next video in the Classroom when playback concludes
- 1 Introduction
- 2 Capabilities
- 3 Use Cases
- 4 Who I am
- 5 Context on investigations
- 6 Selfidentified
- 7 Questions
- 8 Example
- 9 High Level Questions
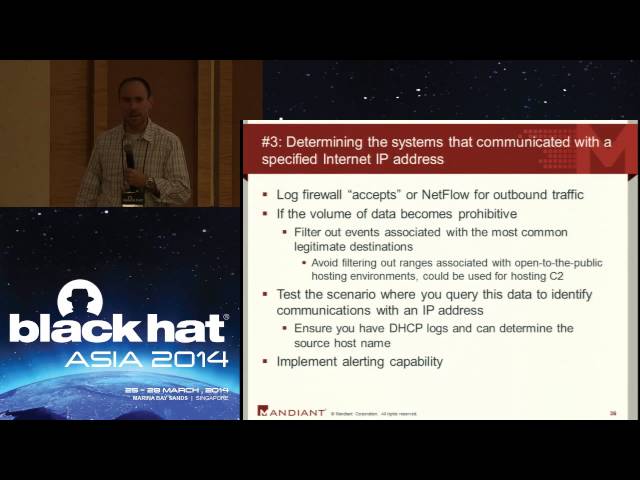
- 10 Data Points
- 11 DHCP Logging
- 12 Systems
- 13 Bottom Line
- 14 Life Cycle
- 15 Possible explanations
- 16 Kerberos service tickets
- 17 Commercial Sim example
- 18 Windows 2003 vs Windows 2008
- 19 Logging Authentication Events
- 20 Events to Log
- 21 Net Float
- 22 Tracking DNS Resolutions
- 23 The Simple Case
- 24 Logging DNS
- 25 Identifying indicators of compromise
- 26 Network indicators of compromise
- 27 Summary
- 28 QA