Completed
Intro
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
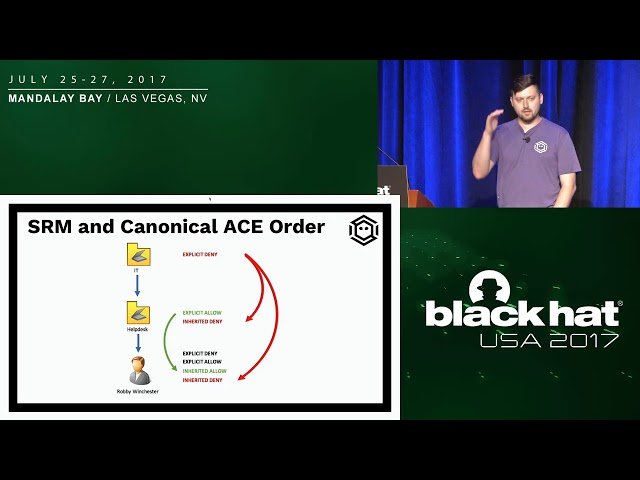
An ACE Up the Sleeve - Designing Active Directory DACL Backdoors
Automatically move to the next video in the Classroom when playback concludes
- 1 Intro
- 2 Disclaimer
- 3 Why Care?
- 4 Previous Work
- 5 DS_CONTROL_ACCESS
- 6 SRM and Canonical ACE Order
- 7 Elevation vs. Persistence
- 8 Target: User Objects
- 9 Target: Group Objects
- 10 Target: Computer Objects
- 11 Target: Domain Objects
- 12 AD Generic Rights
- 13 AD Control Rights
- 14 BloodHound Analysis
- 15 Objective
- 16 Stealth Primitive
- 17 Primitives: Summary
- 18 A Hidden DCSync Backdoor
- 19 Admin SDHolder
- 20 Domain user can access AdmPwd! LAPS cmdlet doesn't detect it!
- 21 Exchange Strikes Back
- 22 Event Logs
- 23 Replication Metadata
- 24 Future Work