Completed
EU anti-US privacy regulations Organization being hit with multiple six-figure fines for violating EU privacy regulations: • Org does not a centralized way to track new/changing Internet assets for E…
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
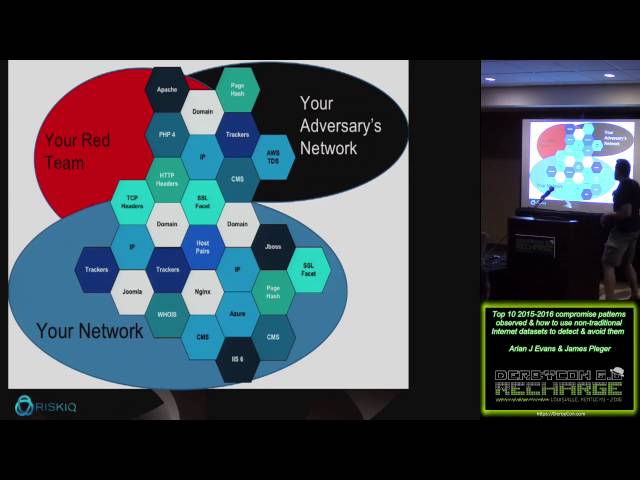
Top 10 Compromise Patterns Observed - How to Use Non-Traditional Internet Datasets
Automatically move to the next video in the Classroom when playback concludes
- 1 Intro
- 2 Pre-owned acquisitions 8. 3rd party hosted marketing campaigns 9. Dev: new app our test system in the cloud 10. IT Automation: cloud backup or replication 11. EU anti-US business regulatory attacks
- 3 3rd Party hosted marketing campaigns Marketing budgets do not align with IT budgets. So when marketing is in a hurry... • Their creatives partners always offer hosting somewhere • Almost guaranteed t…
- 4 Dev: new app/test system in cloud Everyone has new apps & tests systems going into the cloud, Github, etc.... Not in existing ASNS or IP space Can be hard to find until tied to public DNS records Oft…
- 5 IT Automation: cloud backup & replication IT decides to use Glacier or auto-replicate systems to the cloud for disaster recovery... • It doesn't tell security • It doesn't do security Default or weak…
- 6 EU anti-US privacy regulations Organization being hit with multiple six-figure fines for violating EU privacy regulations: • Org does not a centralized way to track new/changing Internet assets for E…
- 7 Malvertising: big bucket of badness Malvertising comprises a wide variety of attack types & targets - we have entire presentations on this, but highlights: . Most are shotgun/fake software attacks • …
- 8 3rd Party Web Components Attackers like SEA increasingly target 3d Party infrastructure like CDNs and marketing widgets hosted offdomain. • Usually targeting 3rd parties embedded in the DOM, as JS or…