Completed
38C3 - Attack Mining: How to use distributed sensors to identify and take down adversaries
Class Central Classrooms beta
YouTube videos curated by Class Central.
Classroom Contents
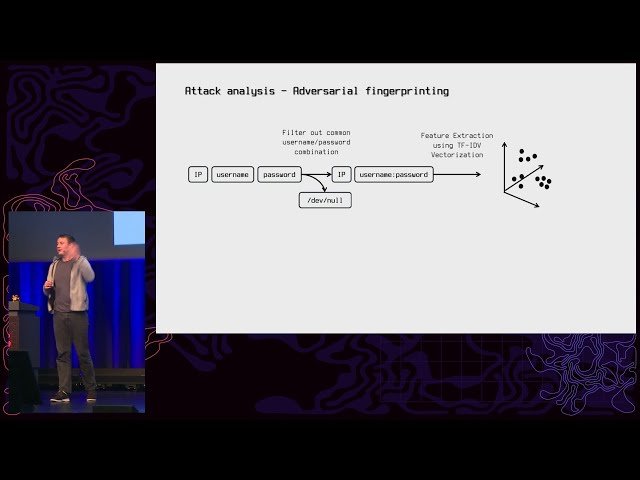
Attack Mining: Using Distributed Sensors to Identify and Take Down Cyber Adversaries
Automatically move to the next video in the Classroom when playback concludes